How Your Phone Camera Can Be Used to Spy on You
According to alleged NSA documents, your smartphone camera could be turned on without your knowledge.
 Credit:
Credit:
Recommendations are independently chosen by Reviewed's editors. Purchases made through the links below may earn us and our publishing partners a commission.
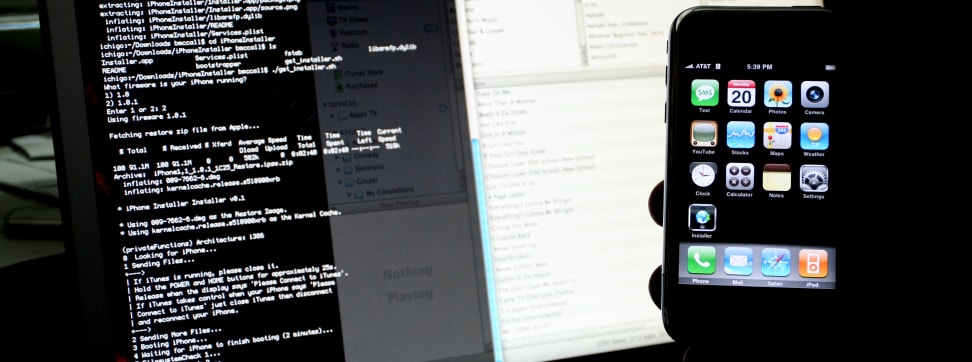
In his recent television interview with NBC's Brian Williams, former NSA analyst Edward Snowden outlined the kind of spying techniques government agencies are capable of.
One segment was particularly troubling. In it, Snowden described how a hacker could potentially hijack the camera in Williams' pre-paid smartphone and use it to capture photos, video, and audio without his knowledge.
But is something like that really possible? Can someone really activate your camera without your consent? Several recent revelations seem to suggest that the answer is yes.

Back in December, German news magazine Der Speigel published alleged NSA documents that it claimed were sent by Snowden. Buried in those documents, which date back to 2008, was mention of a method for gaining complete access to iPhones, dubbed DROPOUTJEEP. (It's important to note, however, that it's impossible to know whether the same methods apply to current iPhone models.)
Apple responded to the allegations in a statement to AllThingsD, claiming that it has "never worked with the NSA to develop a backdoor in any of [its] products, including the iPhone."
According to the alleged NSA documents:
"DROPOUTJEEP is a software implant for the Apple iPhone that utilizes modular mission applications to provide specific SIGINT functionality. This functionality includes the ability to remotely push/pull files from the device, SMS retrieval, contact list retrieval, voicemail, geolocation, hot mic, camera capture, cell tower location, etc. [...] All communications with the implant will be covert and encrypted."
According to the documents, the initial release of DROPOUTJEEP was to be installed via "close access methods," which All Things D interpreted as direct physical access to the device in question. The slide, now more than six years old, said that future versions of this hack would focus on developing the ability to install the exploit remotely.
But if you don't have an iPhone, you're fine... right? No, not quite.
The same documents also claim that the NSA has (or, more likely, had) a special working group dedicated to accessing Blackberry devices, though there's no specific mention of means for activating the camera on a Blackberry. Of course, since 2008 Blackberry has fallen and Android has risen to control more than 80% of the smartphone market. It seems safe to assume that hacks like these are also being developed for Google's OS.
Indeed, just a few days ago Szymon Sidor—whose LinkedIn page states that he's a former engineering intern with the Google Analytics team—demonstrated in a video how it's possible to activate the camera on an Android device remotely. The only visible evidence that the camera application is running is a single pixel that's almost impossible to detect, even if you know it's there.
Though this new video isn't proof that the NSA has access to Android phones, it's strong evidence that they could. With that said, it's important to remember that this type of hacking must be done on a targeted basis. It's extremely unlikely that such an exploit is running on your phone now.
Either way, it's clear that—at least at one point—government agencies had the ability to remotely view the world through private individuals' smartphone cameras.
Hero Image: Flickr user "bwana" (CC BY-NC-SA 2.0)